Introduction
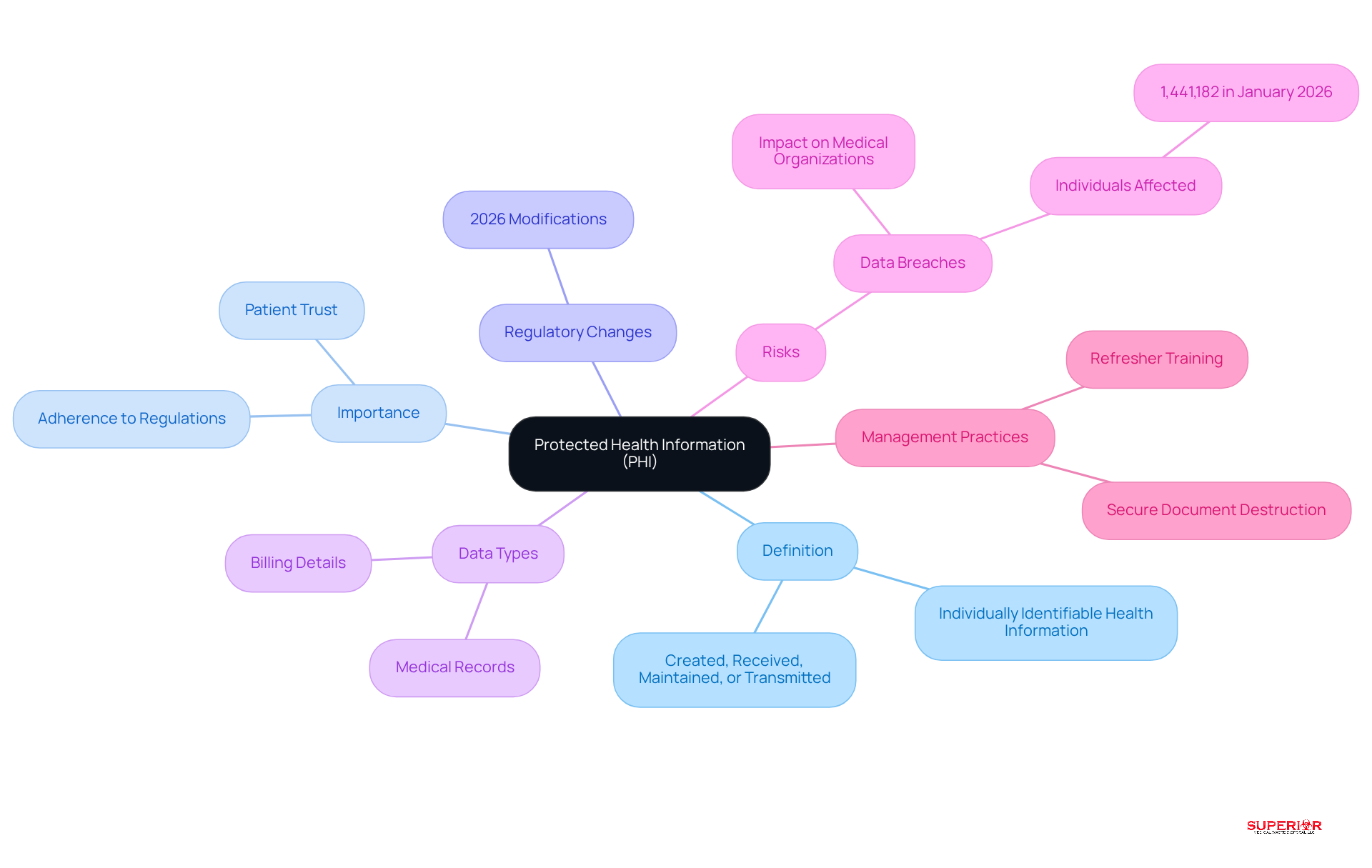
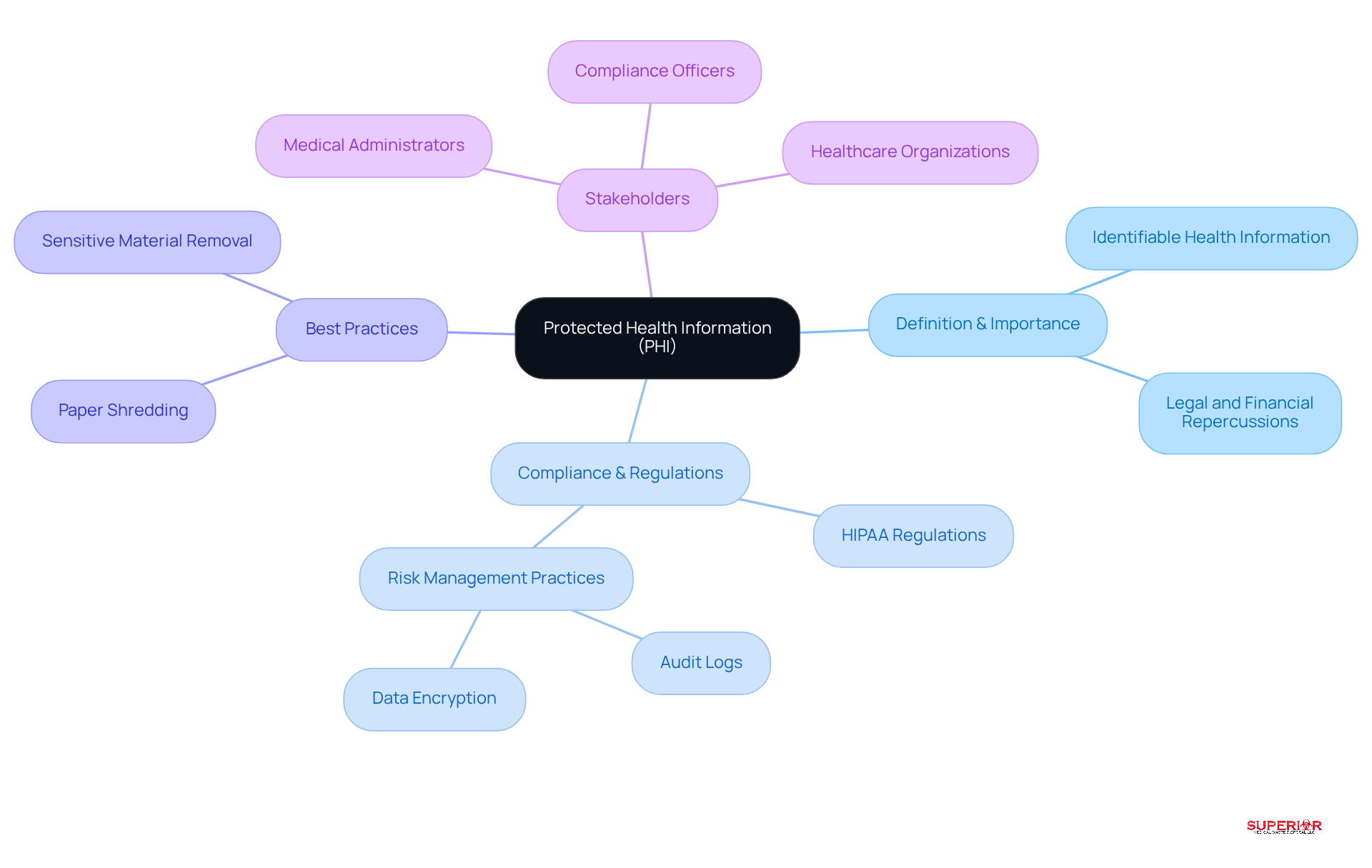
Navigating the complexities of Protected Health Information (PHI) is a critical challenge for healthcare administrators in an era marked by stringent privacy regulations and increasing data breaches. The significance of PHI extends beyond mere compliance; it embodies the trust patients place in healthcare systems to safeguard their most sensitive information. As data breaches become more frequent and regulations continue to change, administrators face significant challenges in safeguarding PHI. Failure to implement robust strategies could lead to severe compliance issues and a breach of patient trust. This article will explore ten key insights that clarify the meaning of PHI in healthcare, providing essential strategies for administrators to improve compliance, reduce risks, and cultivate a security-focused culture within their organizations.
Define Protected Health Information (PHI) in Healthcare
For healthcare administrators, grasping the phi healthcare meaning is vital, especially in light of evolving privacy regulations. PHI includes any individually identifiable health information created, received, maintained, or transmitted by medical providers, health plans, or health clearinghouses. This encompasses a wide range of data, including medical records, billing details, and any information that can identify a patient.
For medical administrators, understanding the phi healthcare meaning is essential not only for ensuring adherence to regulations but also for protecting patient privacy. In 2026, the phi healthcare meaning is underscored by recent modifications to health privacy regulations, which have tightened the conditions regarding the use and sharing of PHI, especially for vulnerable groups.
Effective management of phi healthcare meaning is essential to mitigate risks associated with data breaches, which can severely impact medical organizations, as evidenced by the 1,441,182 individuals affected by breaches in January 2026. A critical aspect of protecting PHI involves the secure destruction of sensitive documents, often referred to as document shredding, secured document destruction, or sensitive material removal. This process is essential for adherence to regulations, which, although not specifically outlining shredding practices, stress the necessity for reasonable and suitable measures to protect the phi healthcare meaning.
By prioritizing PHI regulations and implementing refresher training for workforce members when policies change, administrators can enhance operational efficiency and foster trust within their healthcare facilities. Ultimately, neglecting the phi healthcare meaning regulations can jeopardize patient trust and the integrity of healthcare organizations.
Identify the 18 HIPAA Identifiers That Create PHI
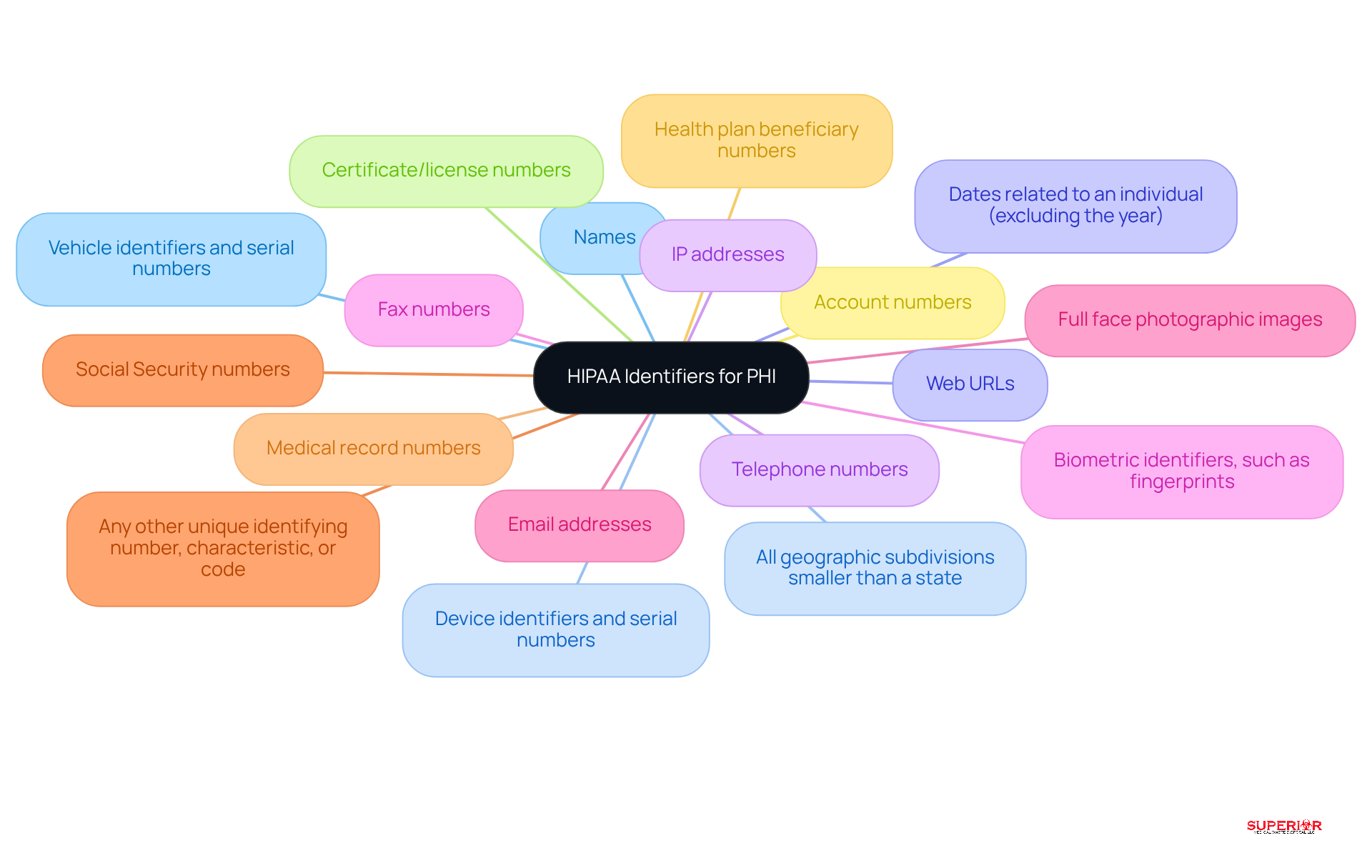
Understanding the 18 identifiers that constitute Protected Health Information (PHI) is essential for grasping the PHI healthcare meaning in compliance and risk management. These identifiers include:
- Names
- All geographic subdivisions smaller than a state
- Dates related to an individual (excluding the year)
- Telephone numbers
- Fax numbers
- Email addresses
- Social Security numbers
- Medical record numbers
- Health plan beneficiary numbers
- Account numbers
- Certificate/license numbers
- Vehicle identifiers and serial numbers
- Device identifiers and serial numbers
- Web URLs
- IP addresses
- Biometric identifiers, such as fingerprints
- Full face photographic images
- Any other unique identifying number, characteristic, or code
Knowing these identifiers helps ensure compliance with privacy regulations and manage risks effectively. Neglecting these identifiers can expose organizations to serious compliance risks and potential penalties.
Understand the Consequences of PHI Breaches
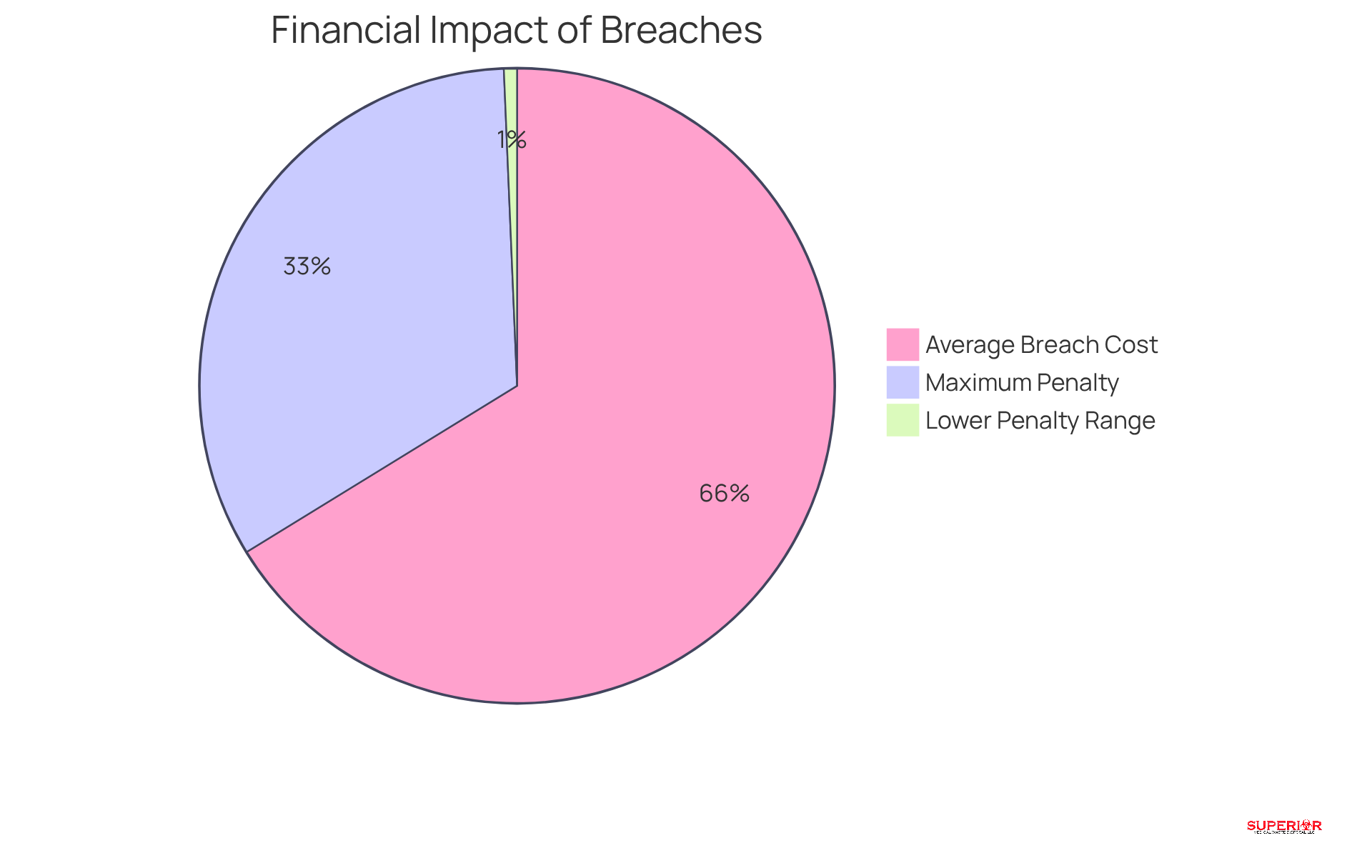
Breaches of protected health information (PHI) pose serious risks that extend beyond immediate financial penalties. The repercussions can be profound, encompassing substantial fines, legal consequences, and significant harm to an organization’s reputation. Under HIPAA regulations, penalties for violations can range from $100 to $50,000 per incident, with a maximum annual penalty reaching up to $1.5 million. Moreover, the financial implications are exacerbated by the potential erosion of patient trust, which is vital for the sustainability of healthcare organizations.
For instance, the OCR reported a notable increase in enforcement actions, with 21 penalties imposed in 2025, reflecting a 31% rise from the previous year. This trend underscores the necessity for medical facilities to prioritize robust practices that reflect the PHI healthcare meaning in management.
Furthermore, case studies show that organizations experiencing breaches frequently incur expenses considerably greater than the average, with medical breaches costing around $10.22 million per incident in 2026, the highest costs reported among all industries for 14 consecutive years. These statistics emphasize the urgent need for medical administrators to implement comprehensive strategies that protect the PHI healthcare meaning and reduce the risks associated with breaches.
Ensure Compliance with HIPAA Regulations Regarding PHI
Healthcare organizations face significant challenges in ensuring compliance with HIPAA regulations, particularly concerning the phi healthcare meaning of Protected Health Information (PHI). To navigate these challenges, they must adopt several essential practices:
- Conduct Regular Risk Assessments: Regular evaluations are key to spotting vulnerabilities in systems and processes, allowing organizations to proactively address potential risks to PHI. This includes maintaining a detailed inventory of IT assets and conducting periodic security assessments.
- Develop and Enforce Comprehensive Privacy Policies: Organizations should create clear, detailed privacy policies that outline how PHI is handled, shared, and protected. These policies must be regularly updated to reflect the phi healthcare meaning of changes in regulations and best practices.
- Continuous training is essential for all employees to ensure they understand privacy regulations and the phi healthcare meaning, which emphasizes the importance of protecting PHI. Regular training sessions should cover foundational privacy policies and job-specific procedures.
- Implement Administrative, Physical, and Technical Safeguards: A multi-layered approach to security is necessary. Administrative safeguards include appointing a HIPAA security officer and conducting risk analyses. Physical safeguards involve securing areas where PHI is stored, while technical safeguards require encryption of ePHI and the use of multi-factor authentication (MFA) to control access.
- Establish Protocols for Reporting and Responding to Breaches: Organizations must have clear procedures in place for reporting breaches and responding to incidents. This includes documenting all access to PHI and maintaining an incident response plan that is regularly tested.
Routine audits and updates to regulatory programs are essential. They help organizations adjust to changing regulations, including the approaching February 16, 2026 deadline for revised Notices of Privacy Practices. Failure to adopt these best practices could lead to severe consequences, including legal penalties and diminished patient trust.

Implement Best Practices for Protecting PHI, Including Secure Document Destruction
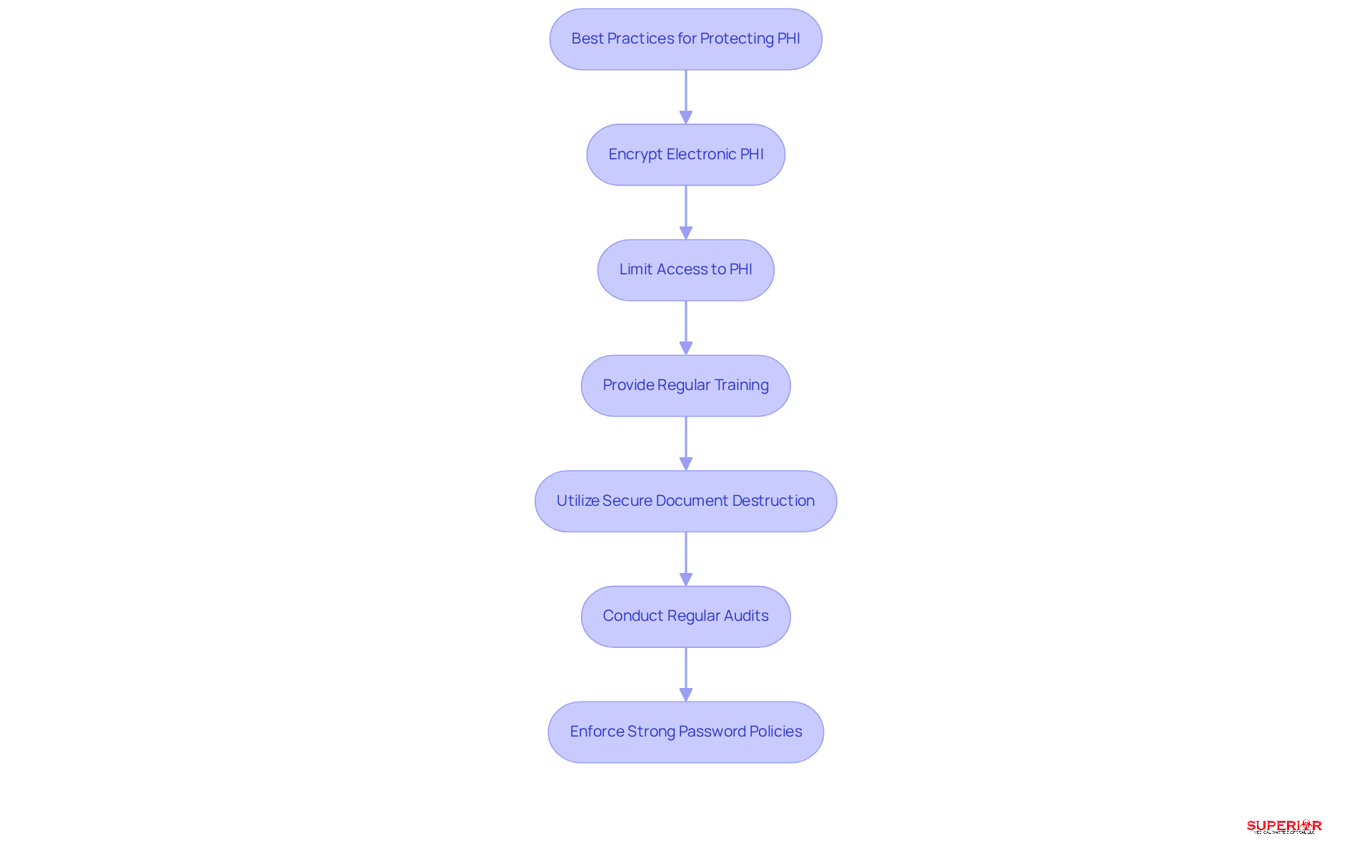
Protecting patient health information (PHI) is a critical responsibility for medical administrators, as understanding the PHI healthcare meaning is essential to avoid serious consequences from lapses. To effectively protect PHI healthcare meaning, medical administrators should implement several key strategies, starting with:
- Encrypting electronic PHI to ensure data integrity.
- Limiting access to PHI to reduce exposure risks and ensure that only authorized personnel have access.
- Providing regular training for staff on proper PHI handling to promote a culture of adherence.
- Utilizing secure methods for document destruction, such as cross-cut shredding or incineration, to ensure that documents are rendered unreadable and irrecoverable.
- Conducting regular audits of PHI access and usage to help identify potential vulnerabilities.
- Enforcing strong password policies along with multi-factor authentication to enhance overall security.
By prioritizing these strategies, organizations can significantly reduce their risk of data breaches and uphold their commitment to patient confidentiality.
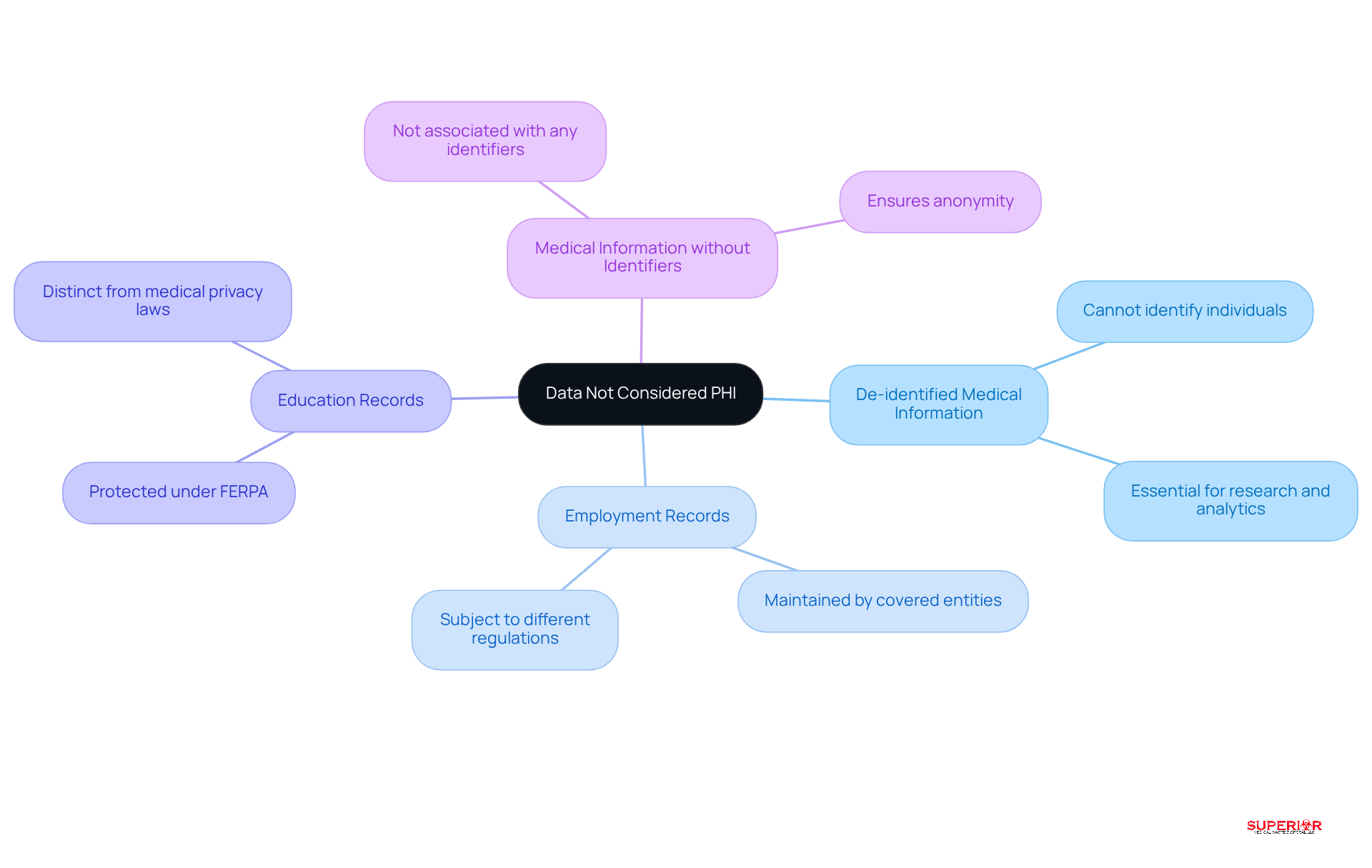
Clarify What Is Not Considered PHI
Understanding the nuances of data classification is essential for organizations aiming to manage the [PHI healthcare meaning](https://superiorwastedisposal.com) effectively. Data that is not classified as PHI includes:
- De-identified medical information, which cannot be used to identify an individual and is essential for research and analytics.
- Employment records maintained by a covered entity in its role as an employer, which are subject to different regulations.
- Education records protected under the Family Educational Rights and Privacy Act (FERPA), which are distinct from privacy laws in the medical field.
- Medical information that is not associated with any identifiers, ensuring that it cannot be traced back to an individual.
Understanding these differences is vital for organizations to enhance their [compliance efforts](https://hipaajournal.com/new-hipaa-regulations) and mitigate risks associated with PHI management.
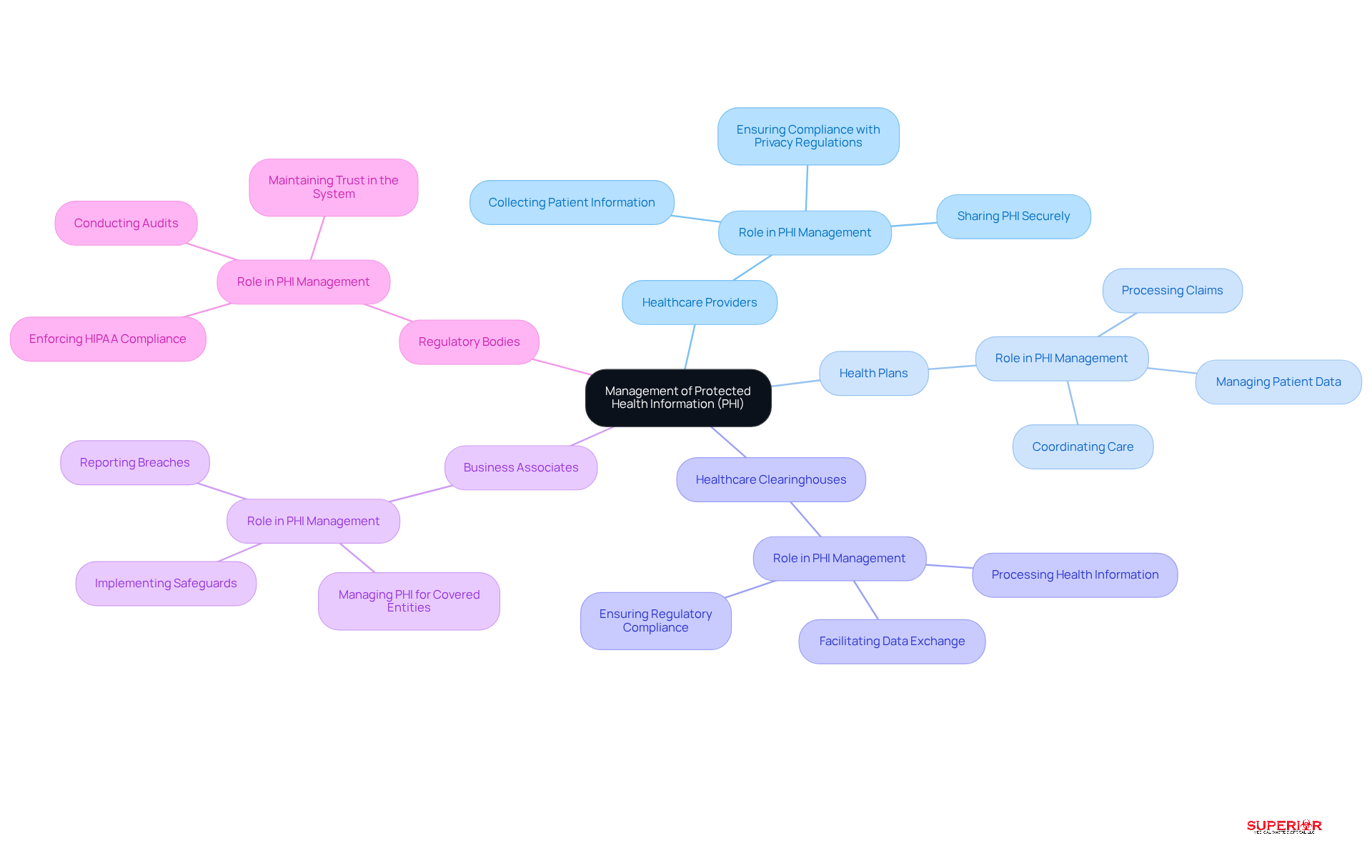
Explore Who Uses and Manages PHI in Healthcare
The safeguarding of Protected Health Information (PHI) highlights the phi healthcare meaning, involving a complex network of stakeholders, each playing a crucial role in compliance and security. Key stakeholders include:
- Healthcare Providers: This group encompasses doctors, nurses, and clinics that directly handle patient information during care delivery. Healthcare providers must ensure that the phi healthcare meaning is upheld through the proper collection, storage, and sharing of PHI in line with privacy regulations.
- Health Plans: Insurance companies manage patient data related to coverage and claims. They play a vital role in safeguarding the phi healthcare meaning while processing claims and coordinating care.
- Healthcare Clearinghouses: These entities process health information, facilitating the exchange of data between providers and payers. They ensure that the phi healthcare meaning is transmitted securely and accurately, adhering to regulatory standards.
- Business Associates: Vendors that manage PHI for covered entities, like billing firms and IT service providers, must adhere to privacy regulations. Their responsibilities include implementing safeguards to protect the phi healthcare meaning and promptly reporting any breaches.
- Regulatory Bodies: Government agencies enforce HIPAA adherence, conducting audits and investigations to ensure that all stakeholders follow privacy and security standards. Regulatory bodies play a crucial role in maintaining trust in the system, which is essential to understanding phi healthcare meaning.
Each stakeholder’s role is interconnected, and effective collaboration among them is vital for the secure management of PHI, which is essential in understanding phi healthcare meaning. For example, medical service providers frequently collaborate with business partners to ensure that data management practices satisfy regulatory standards. This collaboration not only enhances data security but also leads to improved patient care outcomes.
Grasping these roles is essential for healthcare facility administrators to understand the phi healthcare meaning, which helps mitigate risks and foster a culture of compliance and security within their organizations. Furthermore, the possible repercussions of privacy violations, such as fines and harm to reputation, highlight the significance of following these regulations. Organizations must also implement robust data-sharing protocols, including obtaining patient consent and using de-identified data when sharing, to enhance compliance and protect patient privacy while understanding phi healthcare meaning.
Moreover, the secure destruction of sensitive documents is a critical aspect of protecting phi healthcare meaning. Types of information that must be shredded include patient medical records, hard drives, and any documents containing individually identifiable health information, such as Social Security numbers, account numbers, and biometric identifiers. As Roger Shindell, CEO of Carosh Compliance Solutions, emphasizes, “Establishing Business Associate Agreements (BAAs) is a fundamental and critical step in effectively managing third-party risks under HIPAA.
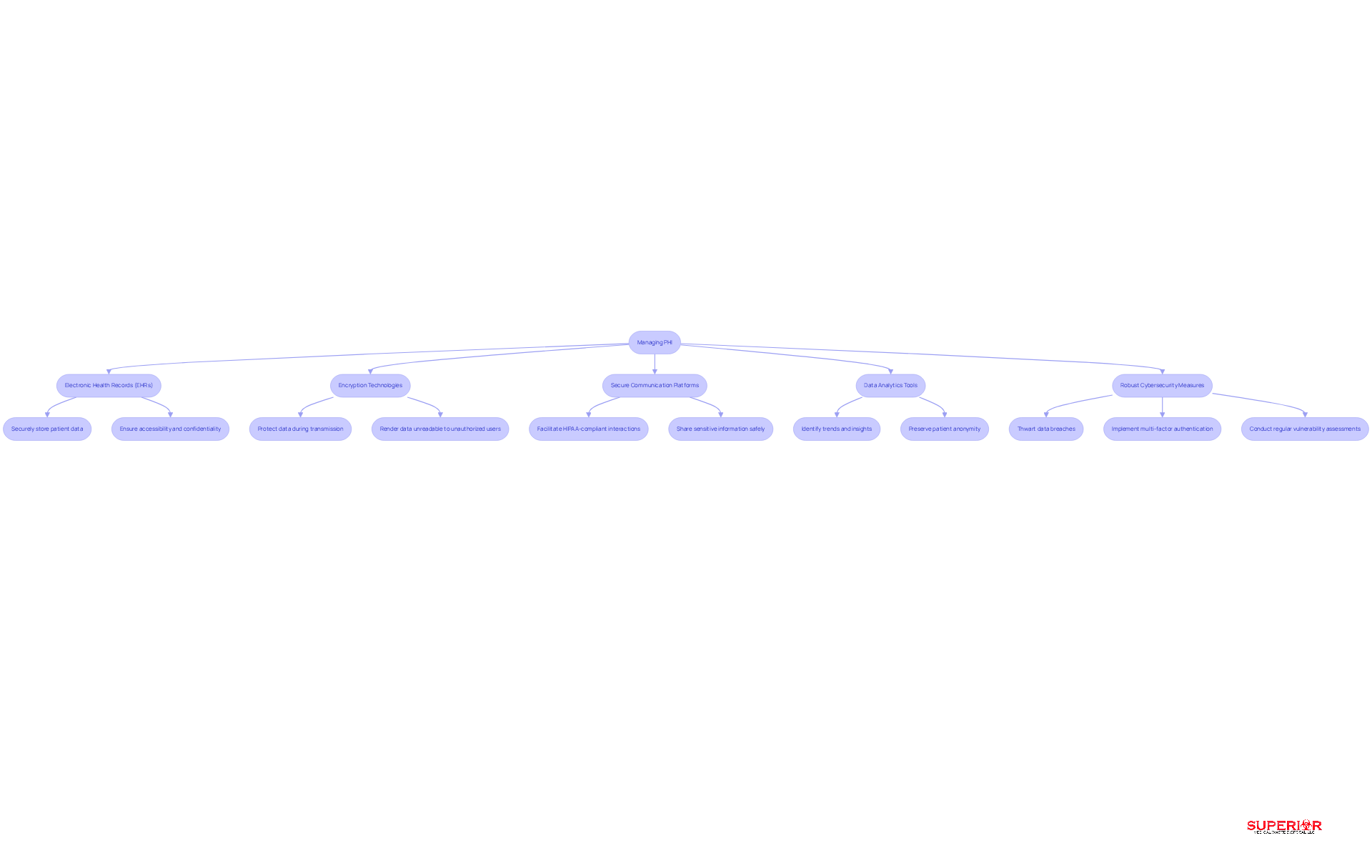
Examine the Role of Technology in Managing PHI
In an era where data breaches are increasingly common, the phi healthcare meaning underscores the critical importance of safeguarding Protected Health Information (PHI) for medical organizations. Technology plays a vital role in this effort. Key advancements include:
- Electronic Health Records (EHRs) that securely store patient data, ensuring accessibility while maintaining confidentiality.
- Encryption technologies that protect data during transmission, rendering it unreadable to unauthorized users.
- Secure communication platforms that facilitate HIPAA-compliant interactions, allowing healthcare professionals to share sensitive information safely.
- Data analytics tools that identify trends and insights while preserving patient anonymity.
- Robust cybersecurity measures designed to thwart data breaches, including multi-factor authentication and regular vulnerability assessments.
Secure document shredding services also play a vital role in protecting sensitive health information. They ensure that documents with individually identifiable health information, like patient medical records and social security numbers, are destroyed securely. Recent statistics show that organizations using multi-factor authentication can cut unauthorized access risks by nearly 99%.
Despite these advancements, the threat of unauthorized access looms large, challenging organizations to stay ahead of potential breaches. Ongoing training and strict adherence to security protocols are essential. Regular audits and risk evaluations are crucial to guarantee compliance and improve the overall cybersecurity stance.
Steve Alder notes that the rapid adoption of technology in healthcare and insurance has made compliance increasingly complex. This highlights the need for continuous education and training, including onboarding and annual refreshers for staff, to maintain a strong security culture. Ultimately, the commitment to ongoing education and stringent security measures will determine the resilience of healthcare organizations against evolving threats.
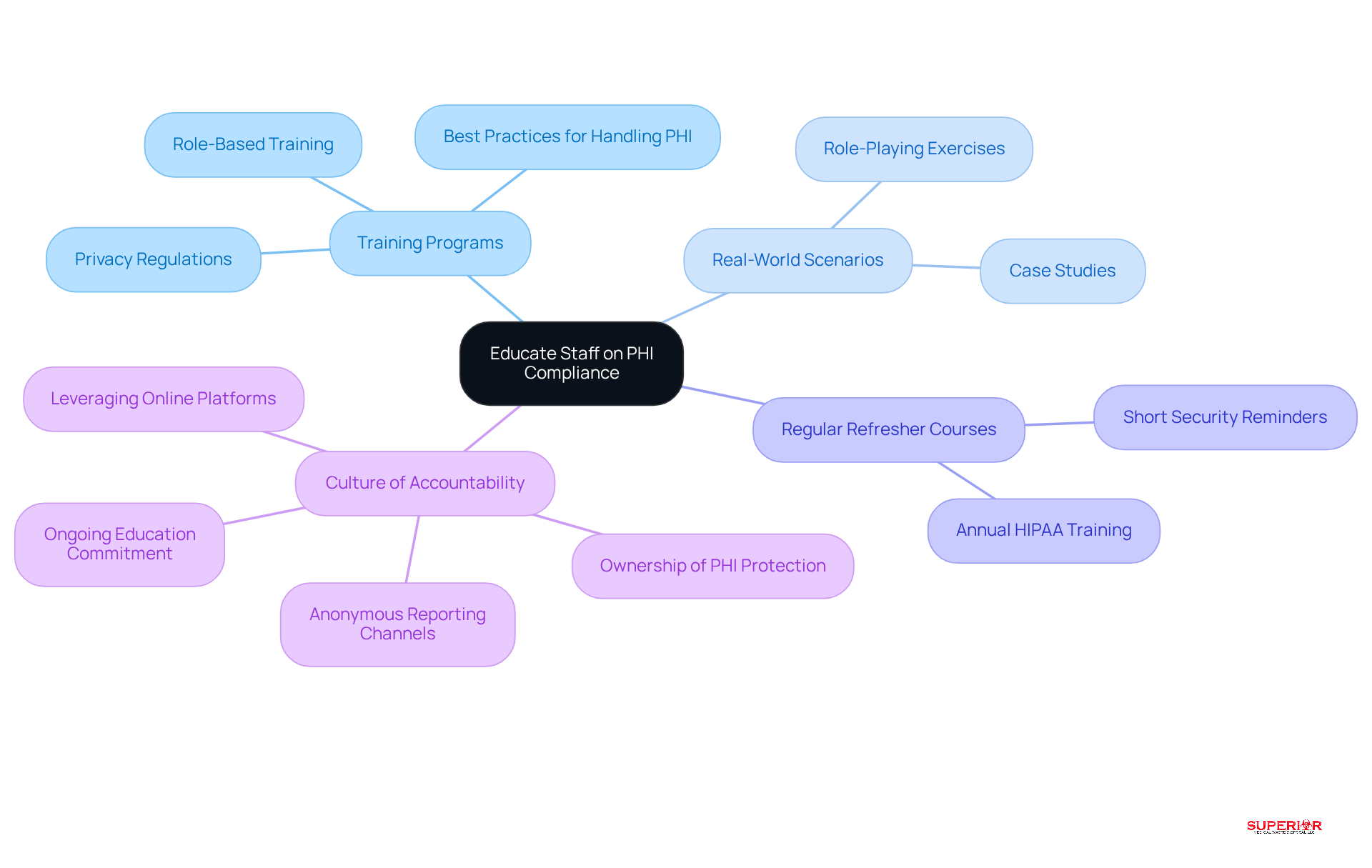
Educate Staff on PHI Compliance and Best Practices
Navigating the complexities of PHI adherence presents significant challenges for healthcare personnel, necessitating a robust educational strategy. Organizations should develop comprehensive training programs that encompass privacy regulations and [best practices for handling PHI](https://www.superiorwastedisposal.com/10-essential-facts-about-red-biohazard-bags-for-healthcare-admins/).
- Incorporating real-world scenarios and role-playing exercises can illustrate adherence challenges and enhance understanding.
- Regular refresher courses are essential to ensure staff remain informed about evolving best practices and regulatory updates.
- Additionally, fostering a culture of accountability encourages staff to take ownership of their role in protecting PHI.
- Leveraging online training platforms provides flexible and accessible learning opportunities.
Ultimately, a commitment to ongoing education not only safeguards patient information but also fortifies the organization’s reputation and compliance standing.
Summarize Key Insights on PHI for Healthcare Administrators
Understanding the complexities of Protected Health Information (PHI) and the phi healthcare meaning is essential for medical administrators to ensure compliance and safeguard patient data. The phi healthcare meaning encompasses any identifiable health information that requires protection, and the 18 HIPAA identifiers clearly define what constitutes PHI. Breaches can lead to significant legal and financial repercussions, making adherence to HIPAA regulations crucial for safeguarding patient information.
Implementing best practices, such as:
- Paper shredding
- Sensitive material removal
is essential for protecting the phi healthcare meaning, particularly regarding documents containing sensitive information like patient medical records and Social Security numbers. Additionally, recognizing what does not qualify as PHI can streamline compliance efforts.
The management of PHI involves multiple stakeholders, and understanding the phi healthcare meaning is crucial as technology enhances security while also posing threats to PHI. Ongoing staff education is vital for maintaining compliance. Ultimately, understanding the phi healthcare meaning is crucial as the proactive management of PHI not only protects patient privacy but also fortifies the integrity of healthcare organizations.
Conclusion
Healthcare administrators face significant challenges in managing Protected Health Information (PHI) while ensuring compliance and safeguarding patient data. The meaning of PHI encompasses a range of identifiable health information that requires stringent safeguarding measures. As healthcare regulations evolve, the significance of adhering to these standards becomes increasingly apparent, highlighting the need for effective strategies and ongoing training.
Throughout the article, key insights have been highlighted, including:
- The identification of the 18 HIPAA identifiers that constitute PHI
- The serious consequences of data breaches
- The importance of implementing best practices for protecting sensitive information
Furthermore, the roles of various stakeholders in managing PHI and the impact of technology on security have been explored, emphasizing the interconnected nature of compliance and effective data management.
By actively managing PHI, healthcare organizations can protect patient privacy and build trust with their communities. By fostering a culture of compliance through ongoing education and the adoption of secure practices, administrators can mitigate risks and uphold the highest standards of patient care. Embracing these insights will empower healthcare leaders to navigate the complexities of PHI effectively, ensuring that patient information remains secure in an ever-changing landscape.
Frequently Asked Questions
What is Protected Health Information (PHI) in healthcare?
Protected Health Information (PHI) includes any individually identifiable health information created, received, maintained, or transmitted by medical providers, health plans, or health clearinghouses. This encompasses medical records, billing details, and any information that can identify a patient.
Why is understanding PHI important for healthcare administrators?
Understanding PHI is crucial for healthcare administrators to ensure adherence to privacy regulations and protect patient privacy. Recent modifications to health privacy regulations have tightened the conditions regarding the use and sharing of PHI.
What are the risks associated with PHI breaches?
PHI breaches can lead to substantial fines, legal consequences, and significant harm to an organization’s reputation. Penalties for violations can range from $100 to $50,000 per incident, with a maximum annual penalty of up to $1.5 million.
How many individuals were affected by data breaches in January 2026?
In January 2026, 1,441,182 individuals were affected by data breaches.
What are the 18 HIPAA identifiers that create PHI?
The 18 HIPAA identifiers include: 1. Names 2. All geographic subdivisions smaller than a state 3. Dates related to an individual (excluding the year) 4. Telephone numbers 5. Fax numbers 6. Email addresses 7. Social Security numbers 8. Medical record numbers 9. Health plan beneficiary numbers 10. Account numbers 11. Certificate/license numbers 12. Vehicle identifiers and serial numbers 13. Device identifiers and serial numbers 14. Web URLs 15. IP addresses 16. Biometric identifiers (e.g., fingerprints) 17. Full face photographic images 18. Any other unique identifying number, characteristic, or code.
What are the financial implications of PHI breaches?
Medical breaches can cost around $10.22 million per incident in 2026, making them the highest costs reported among all industries for 14 consecutive years. Additionally, breaches can erode patient trust, which is vital for the sustainability of healthcare organizations.
What measures can healthcare administrators take to protect PHI?
Healthcare administrators can protect PHI by implementing secure destruction of sensitive documents, conducting refresher training for workforce members when policies change, and prioritizing adherence to PHI regulations to enhance operational efficiency and foster trust.
List of Sources
- Define Protected Health Information (PHI) in Healthcare
- HIPAA (https://ama-assn.org/practice-management/hipaa)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- January 2026 Healthcare Data Breach Report (https://hipaajournal.com/january-2026-healthcare-data-breach-report)
- Identify the 18 HIPAA Identifiers That Create PHI
- The 18 HIPAA Identifiers : Loyola University Chicago (https://luc.edu/its/aboutus/itspoliciesguidelines/hipaainformation/the18hipaaidentifiers)
- Human Research Protection Program | UC Berkeley (https://cphs.berkeley.edu/hipaa/hipaa18.html)
- 18 HIPAA Identifiers for PHI (https://compliancy-group.com/18-hipaa-identifiers-for-phi)
- What You Need to Know About PHI Identifiers – LuxSci (https://luxsci.com/know-phi-identifiers)
- What are the 18 HIPAA Identifiers? – Pilot Digital (https://pilotdigital.com/blog/what-are-the-18-hipaa-identifiers)
- Understand the Consequences of PHI Breaches
- Healthcare Data Breach Statistics 2026: Costs, HIPAA Fines & Trends (https://medhacloud.com/blog/healthcare-data-breach-statistics-2026)
- 40 HIPAA Compliance Statistics for 2026 — Fines & Breach Data (https://medhacloud.com/blog/hipaa-compliance-statistics-2026)
- 51 HIPAA Statistics Every Healthcare Entity Needs to Know in 2026 | UpGuard (https://upguard.com/blog/hipaa-statistics)
- February 2026 Healthcare Data Breach Report (https://hipaajournal.com/february-2026-healthcare-data-breach-report)
- 60+ Healthcare Data Breach Statistics for 2026 (https://brightdefense.com/resources/healthcare-data-breach-statistics)
- Ensure Compliance with HIPAA Regulations Regarding PHI
- HIPAA Compliance Update: What Must Be Done by February 16, 2026 (https://americanmedicalcompliance.com/general/hipaa-compliance-update-what-must-be-done-by-february-16-2026)
- 2026 HIPAA Compliance Guide: NPP Updates & Penalty Tiers (https://hellonote.com/2026-hipaa-compliance-guide-therapy-practices)
- The New Compliance Baseline: How HIPAA 2.0 Changes Everything – Intelisys (https://intelisys.com/security-compliance-healthcare-hipaa)
- HIPAA Compliance in 2026: Everything You Need to Know (https://venn.com/learn/hipaa-compliance)
- Implement Best Practices for Protecting PHI, Including Secure Document Destruction
- Secure Paper Shredding Guide for Healthcare Professionals – Papersavers Ltd (https://papersavers.ca/shredding/secure-paper-shredding-guide-for-healthcare-professionals)
- HIPAA-Compliant Medical Record Shredding | FileVault (https://filevaultusa.com/blog/hipaa-compliant-medical-record-shredding)
- HIPAA Compliant Medical Record Shredding (https://shrednations.com/articles/hipaa-compliant-medical-record-shredding)
- Best HIPAA-Compliant Paper Shredders for Secure PHI Disposal (https://accountablehq.com/post/best-hipaa-compliant-paper-shredders-for-secure-phi-disposal)
- Secure Shredding & Data Destruction for Healthcare Facilities. – SAFESHRED (https://safeshred.com/secure-shredding-data-destruction-for-healthcare-facilities)
- Clarify What Is Not Considered PHI
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- De-identification of Protected Health Information: 2026 Update (https://hipaajournal.com/de-identification-protected-health-information)
- New HIPAA Regulations in 2026 (https://hipaajournal.com/new-hipaa-regulations)
- HIPAA Compliance 2026: PHI Security & Patient Trust (https://cookie-script.com/privacy-laws/hipaa-guide-2026)
- New HIPAA Requirements for Healthcare: What’s Changed and How to Comply in 2026 (https://accountablehq.com/post/new-hipaa-requirements-for-healthcare-what-s-changed-and-how-to-comply-in-2026)
- Explore Who Uses and Manages PHI in Healthcare
- 2026 Healthcare Privacy Regulations: What’s New and How to Stay Compliant (https://accountablehq.com/post/2026-healthcare-privacy-regulations-what-s-new-and-how-to-stay-compliant)
- The HIPAA compliant way to engage stakeholders (https://hipaatimes.com/the-hipaa-compliant-way-to-engage-stakeholders)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- HHS’ Office for Civil Rights Settles HIPAA Security Rule Investigation with Top of the World Ranch Treatment Center (https://hhs.gov/press-room/ocr-settles-hipaa-security-rule-investigation-twrtc.html)
- Strategic Management of Third-Party Risks in HIPAA Compliance (https://carosh.com/strategic-management-of-third-party-risks-in-hipaa-compliance)
- Examine the Role of Technology in Managing PHI
- Oncology Practice Cybersecurity Checklist: Essential Steps to Protect PHI and Stay HIPAA-Compliant (https://accountablehq.com/post/oncology-practice-cybersecurity-checklist-essential-steps-to-protect-phi-and-stay-hipaa-compliant)
- The Use of Technology and HIPAA Compliance – 2026 Update (https://hipaajournal.com/the-use-of-technology-and-hipaa-compliance)
- 51 HIPAA Statistics Every Healthcare Entity Needs to Know in 2026 | UpGuard (https://upguard.com/blog/hipaa-statistics)
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- HIPAA Security Rule Cybersecurity Changes (https://constangy.com/sp_resources-blogpost-hipaas-next-era-new-rules-for-new-technologies-and-risks)
- Educate Staff on PHI Compliance and Best Practices
- HIPAA Training Frequency Requirements (2026 Update): What You Need to Know (https://accountablehq.com/post/hipaa-training-frequency-requirements-2026-update-what-you-need-to-know)
- HIPAA Training Survey (https://hipaajournal.com/hipaa-training-survey)
- The HIPAA Journal Annual Survey (https://hipaajournal.com/hipaa-journal-annual-survey)
- Continuing staff education should be a priority for healthcare teams (https://ntracts.com/blog/why-continuing-staff-education-should-be-a-priority-for-healthcare-teams)
- Survey Finds Over 90% of Organizations Now Provide Annual HIPAA Refresher Training (https://hipaajournal.com/over-90-of-organizations-now-provide-annual-hipaa-refresher-training)
- Summarize Key Insights on PHI for Healthcare Administrators
- HIPAA (https://ama-assn.org/practice-management/hipaa)
- Latest HIPAA AI Compliance News: Guidance, Enforcement, and What’s Changing (https://accountablehq.com/post/latest-hipaa-ai-compliance-news-guidance-enforcement-and-what-s-changing)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- New HIPAA Regulations in 2026 (https://hipaajournal.com/new-hipaa-regulations)
